
I have just printed my PhD thesis for submission to the University of Cambridge. The title is ‘Militant Islamist radicalisation: does the Internet atomise?’. The following is a summary of the thesis extracted from part of the summary. In a nutshell, I was exploring how ideas traverse the Internet.
![]()
The State is feeling the first shocks of a communications change that will have an impact on security and society for many decades to come.
The analogue engineers of AT&T were faced with a challenge in understanding the digital network ideas that Paul Baran proposed in the early 1960s, described in chapter 2, and proved ultimately unable to cast off their assumptions of centralisation, hierarchy, and control. Not dissimilarly, the policymaking community of the mid 2000s was unable to get to grips with the uncontrollable nature of the new medium, as demonstrated by the censorship initiative considered at European level from 2005–2007, as discussed in chapter 1. It is for this reason that this thesis has studied what happens to a rigorously enforced message when it moves beyond committed militant venues and attempts to proliferate on open fora on the Internet where it may suffer criticism, inaccurate reproduction, or atomisation by other means at the hands of Internet users. This is a question is about the competition between centripetal and centrifugal forces on the Internet. It is also the story of how the vanguard of ‘Internet mujahedeen and media Jihadi Knights’ is faring in the emerging digital world.[8]
The context established in the first chapter of this thesis is of a security problem that poses a genuine threat of violence to citizens on the one hand, but which is poorly understood on the other (as demonstrated by the conflict between major scholars, and the policy community’s inclination to opt for inappropriate censorship solutions). The stakes are high in two respects: first, because the Internet is a valuable high ground in States’ efforts against militant Islamist radicalisation; second, because policy missteps now could limit the benefits that the Internet may introduce for culture, politics, and the economy, which are still at a comparatively early stage.[9] This is especially troubling because militant Islamist content is largely immune to state action in the absence of an international and legally–binding consensus on what constitutes illegal content. As chapter 1 elaborates, the range of current measures all fall prey to the problem of foreign safe havens.
The second chapter describes the Internet as a ‘centrifugal’ medium, introducing this term to denote the peculiar engineering characteristics on which it was built. The premise on which the Internet and the technical protocols that govern communications across it were based explicitly lifted control from the centre and dispersed it everywhere throughout the network so as to make the network robust in the face of a nuclear strike. Rather than there being a single controlling node at the centre, control rested instead within every participating node in the network. This centrifugal redistribution was followed by the development of personal computing and bulletin board systems that further distributed control of communication, and put power literally into the hands of the masses. At the same time the norms that had developed on the early networks were also centrifugal, breaking the formal conventions of one to many communications and creating instead an assertive audience of individuals who compete for attention in informal discussions on the basis of meritocracy rather than by virtue of pre–existing prestige. This laid the foundations for the ‘perpetual beta’ described in chapter 4, and for the atomisation discussed in chapter 6.
The third chapter argues that by virtue of being a centrifugal medium the Internet is a fecund environment for the propagation of militant memes. For example it allows militant propagandists to bypass mainstream media. Yet beyond this obvious aspect, it also allows militant campaigns to leverage the power of peripheral support, rather than relying on the central organisation alone. This is significant because centrifugal campaigns can gain an advantage over conventional campaigns, as demonstrated in mainstream political campaigning. While the Ventura campaign of 1997–98 demonstrated this potential, the Dean and Obama campaigns, which increasingly leveraged the potential of group forming networks, prove the point. This centrifugal advantage is defined in network effects laws, the most appropriate of which is Reed’s 3rd Law of group forming networks. This is all the more powerful because in the context of militant Islamist radicalisation on the Internet, the centre is particularly week, and the Internet’s ability to connect individuals who share so–called ‘long–tail’, or niche, perspectives is among the only ways in which sufficient numbers could form an amorphous community to share and serve these common interests from the periphery. Reed’s 3rd Law takes account of the potential of such communities to produce activist members. These individuals are the product of a culture of initiative that has developed online since the first phreaker communities in the 1960s. Thus the Internet is not only a fecund environment for militant Islamist radicalisation by virtue of its ability to bypass mainstream media, but also because it is a recruiting ground for the next generation of militant media activists such as Younis Tsouli (‘Irhabi 007’) who can perpetuate the message in a ‘leaderless’ strategy.
The fourth chapter deviates from the sobering message of the third. While the Internet is indeed fecund, this chapter argues that it is also hazardous. Indeed the very characteristics that make it fecund also make it hazardous. Because the Internet is centrifugal it has increasingly empowered its users to control how content is disseminated across it. This is particularly true since 2004 when the ‘Web 2.0’ generation of technologies began to enable users to edit media on the most popular websites. User manipulation of online media began to create a situation in which information on the Internet was in a state of having no final edit, in a condition of ‘perpetual beta’. The Internet is making information plastic and malleable in a manner that mass–communications have not been since the introduction of the printing press. This was accompanied by the emergence of a ‘folksonomy’ in which peer opinion carries the weight of authority in the selection and dissemination of worthwhile content on the Internet. Taken together these two changes mean that information is subject to a double hazard of distortion and approval by its intended audience. This hazard does not exist on forums where the members and administrators are committed supporters of the militant Islamist cause. Yet to successfully leverage the fecundity described in the previous chapter, militant propagandists must venture beyond these friendly spaces and expose their narrative to the hazardous conditions of the wider Internet audience. This is the hypotheses of this thesis: al Qaeda’s militant rhetoric will be distorted on forums that are not closely affiliated with al Qaeda. The cohesion of the metaplex is being degraded by the hazard of the perpetual beta over time on web forums, unless they happen to be committed to the preservation of that memeplex.
Chapter five discusses memetics, and uses memetic reproduction as a test of whether the hypothesis expressed in the previous chapter – that the hazard of the Internet distorts the militant message – is true. In order to conduct such a test it is necessary to establish a discrete grouping of memes (a memeplex, in other words) whose longevity as a consistent collection of reoccurring memes is to be tested. The chapter examines Islamist and militant Islamist rhetoric and statements by al Qaeda leaders to identify a discrete number of reoccurring memes. Following a number of tests to verify and refine this memeplex, a memeplex composed of three memes is identified: persecution, precedent, and piety.
The sixth chapter uses data mining of a very large dataset to determine whether the percentage of relevant posts in which this memeplex appears is increasing or decreasing over time. Following a discussion on methods and data preparation the chapter describes the categorisation of web forums in the dataset according to the frequency of their references to officially branded militant media outlets. The chapter concludes with a summary of the results of the data mining (an extended discussion of the statistical results is in the appendix). The results of this process show that uncommitted and mainstream forums have a decreasing trend of memeplex cohesion, while committed forums have an increasing one. These results show that the hazard of the Internet is atomising the militant memeplex hypothesised in chapter 5. Therefore the Internet is fecund in the manner described in chapter 3, but also hazardous in the manner described in chapter 4.
A Chatham House working paper on violent radicalisation on the Internet asked a pivotal question: what is the balance was between medium and message.[10] This thesis finds that the medium is singularly important. The Internet is a medium unlike its predecessors: it is centrifugal, fecund, and hazardous. This is the first time that it has been so described, and the impact of this theory, particularly since this thesis goes on to show evidence that atomisation of the militant rhetoric of bin Laden and the core al Qaeda hierarchy occurs as a result, could have profound consequences for the future of policy. This thesis is intended to serve a practical purpose beyond a general widening and deepening of the larval field of radicalisation research. It is intended to put the Internet, still an unknown and new medium, into a concrete context for policy makers and researchers.
The conclusion that the Internet atomises militant Islamist rhetoric is of pivotal significance for future policy making in this area. Until now the focus of policymaking in Europe in this area has been on the Internet’s potential as a medium of violent radicalisation, as described in chapter 1. This approach focuses on the medium’s fecundity, described in chapter 3, but it fails to take into account the centrifugal character of the medium, expressed in these terms for the first time in chapter 2, and the impact of the perpetual beta, described in chapter 4. The Internet is at once both fecund and hazardous. These characteristics, while a challenge the State’s ability to control information, are also a challenge to the militant Islamists’ ability to reach beyond those forums that they already dominate and to leverage the benefits of network effects. In short, this suggests that the rhetoric of bin Laden and the core hierarchy of al Qaeda is not virulent on the Internet – at least, not on the English speaking Internet. Therefore the challenge is not only to ‘drain the swamp’, but to see whether the waters subside of their own accord.[11] Fecundity and hazard have an antagonistic relationship that means niche communications can form, but also means that the exponential potential of Reed’s 3rd Law is unlikely to be realised.
This allows the problem of violent radicalisation on the Internet to be redefined in a number of ways. First, if the Internet is both fecund and hazardous, and is so in such a manner that the militant narrative does not perpetuate wildly beyond already committed forums, then the Internet does not represent an inordinate threat of violent radicalisation. Second, if the memeplex is generally confined to committed forums it is possible to define and target this problem in a specific and focussed way rather than by Internet–wide measures such as web filtering.
Third, the committed forums are an identifiable and definable target for focussed action. They refer to official militant media outlets, as proven by the data mining test in chapter 6, which indicates the presence of a structured and consistent communication chain.[12] It could be vulnerable to network and link analysis and disruption similar to the strategies attempted against militant groups in previous conflicts.[13] Notwithstanding the problem of safe havens, identified in chapter 1, these forums are sufficiently delineated that, as Aaronn Weisburd points out, they may be vulnerable to disruption by covert means.[14] According to him, only 20% of a wide sample of militant websites active in 2002 – 03 that were removed from their hosting services had resurfaced in 2007.[15] The forums had a 80% mortality rate.[16]
Fourth, the existence of the online world in fact reinforces the importance of taking action offline. The prospect that a small proportion of citizens should be willing to kill their peers is a problem within society, rather than one of technology. Online radicalisation is a symptom of two factors: that the Internet is a medium of networks and relationships; and that there is a fundamental problem within society. Much like counterinsurgency, the issue is ‘not just about ‘their’ politics (i.e. the politics of Afghanistan and Iraq), but also about ‘ours’’.[17] Consider the following anecdote. In June 2009 British soldiers fighting in Afghanistan discovered an Aston Villa Football Club tattoo on the body of a dead militant. ‘It was a shock to hear that the guys we were fighting against supported the same football clubs as us, and maybe even grew up on the same streets as us’.[18]
In short, it is society and citizenship that is at issue. The strength of society persists in a networked world, and off line measures to deal with violent radical sentiment within society should be pursued. Counter narratives need not necessarily be on–line, nor must they be Internet focused. Measures that succeed offline will necessarily make an impact online. It might seem too obvious to state, but the perpetual beta means that the more individuals across society that subscribe to the values of the State offline, the more vulnerable the militant message is to distortion online. Though the challenge is online radicalisation, the focus on off–line society must not be obscured.
It might be a sufficient outcome to give pause to an Internet user who might otherwise have accepted militant rhetoric as fact. If doubt is enough to prevent one from committing or supporting terrorist offences then a strategy to win the Internet high ground should have the objective of injecting a kernel of doubt in the minds of Internet users who have some sympathy with the militant message. While this might not have an impact on the kernel of committed militants the focus of is the wider population of prospective sympathisers occupying chatrooms and web forums. According to a militant recruiting manual, ‘my dear brother, you must know … that one doubt is sufficient to take a person away from the path, especially if the candidate is in the beginning stage’.[19] To achieve this doubt and avoid a younger generation of militants being radicalised to violent action against their peers the State must focus on the off–line health of society. From a UK perspective this resonates with the current thrust of the Prevent strategy of ‘targeted, local work to support people who are most vulnerable to radicalisation and to disrupt propagandists for terrorism’.[20] Since the Prevent strategy is under review and this emphasis may be changed, or expanded upon. The new 2010 national security strategy of the United States also prioritises ‘empowering communities to counter radicalisation’ and notes ‘our best defenses against this threat are well informed and equipped families, local communities, and institutions’.[21] Yet it is important to note that measures targeted explicitly at Muslims, such as the UK Home Office’s Pathfinder Fund, while aimed at empowering communities to act against violent radicalisation, have suffered by their explicit focus on Muslims.[22]
Rather than pursuing a minority politics approach[23] a counter narrative to avert the next generation of violent radicals might apply across society, and could be as broad and non–specific to the radicalisation problem as a school curriculum that instils a sense of citizenship. A UK Conservative Party study recommended in 2007 that a school history curriculum tackling the delicate issue of British colonialism would give both majorities and minorities a clear sense of how they came to be, and why they belong within, their society.[24] A student more secure in their role in their wider society is more likely, one might presume, to have doubts when confronted with violent ideas on the Internet. Such a person might in fact become an agent of the perpetual beta and contribute to the degradation of the militant call to violence online.
It is not the purpose of this conclusion to recommend or propose a specific solution to militant Islamist radicalisation on the Internet. However, a number of guiding principles can be suggested, based on the findings of this research. It is crucial to recognise at this early stage of the Internet’s development that the Net, like the high seas, is part of the global commons, and any official approach to it at this early stage in its development must be considered from the long term perspective of building up a strong society of digital natives rather than by the short term imperative to act in the wake of a terrorist event. In the emerging digital era the State will be unable to control information as it has done in the past. Instead it must increasingly rely on its citizens and on the strength of its society so that the plasticity of information can work in its favour. One must respect the medium, but challenge the message. Centrifugal strategies that empower the individual should be adopted. Subversives will persist online, but the more people in society who understand and oppose the violent narratives that threaten their society, the harder it will be for isolated militants to appeal with a consistent message across the wider Internet.
The data used in the chapter six is from the Dark Web project at the University of Arizona, thanks to Professor Hsinchun Chen. The trend graphs below show bars and trend lines. Bars show the ratio of monthly observations (of percentage of posts containing the memeplex) to all political posts above and below the trend.
Category 1: forum showing rise in memeplex

Category 2 (uncommitted): forum shows declining trend in memeplex
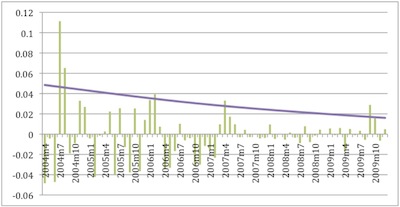
(note: Not all category 2 forums showed so steep a decline.)
Category 3 (mainstream): forum shows declining trend in memeplex

2 thoughts on “PhD thesis summary”